Cybersecurity is a growing concern in today’s digital age. In this blog post, we will explore some of the most common types of cyber attacks that individuals and organizations face. Common types of cyber attacks include:
- Phishing Attacks
- Malware Attacks
- Man-in-the-Middle Attacks
- Denial-of-Service Attacks
- SQL Injection Attacks
- Zero-Day Exploits
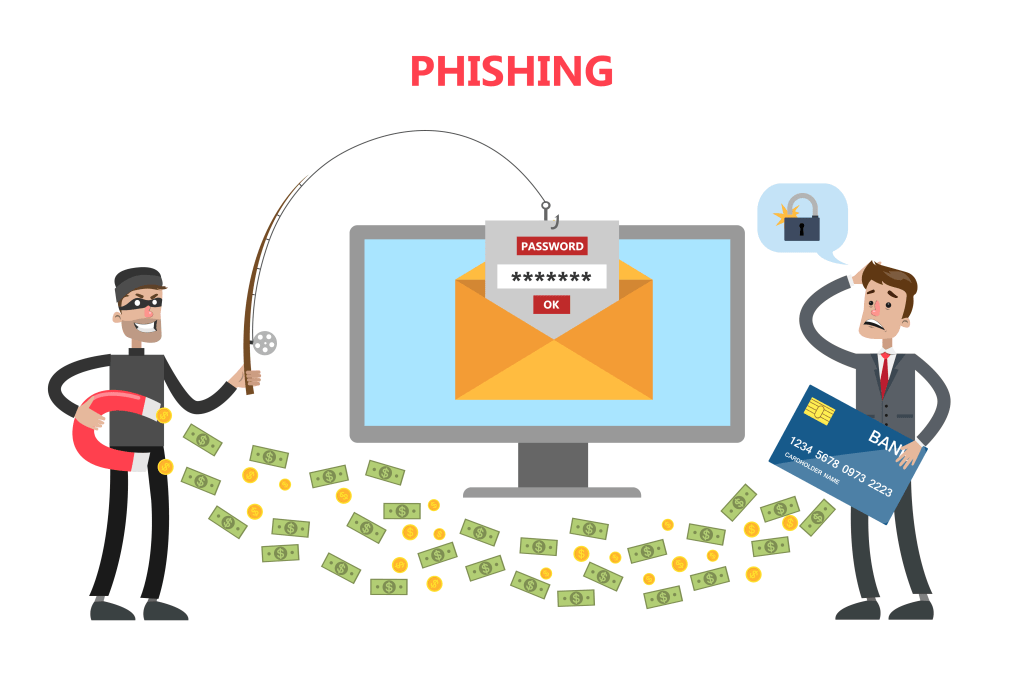
Phishing Attacks: Cyber Attacks
Phishing is a cyber attack where attackers impersonate legitimate organizations or individuals to trick victims into revealing sensitive information. This could be login credentials, credit card numbers, or other personal information. Phishing attacks often occur via email, where the attacker sends a message that appears to be from a trusted source.
Types of Phishing Attacks
There are several types of phishing attacks, each with its unique characteristics:
- Email Phishing: This is the most common type of phishing attack. The attacker sends an email that appears to be from a trusted source, such as a bank or a popular website, and asks the recipient to provide sensitive information.
- Spear Phishing: This is a targeted form of phishing where the attacker tailors their message to a specific individual or organization. The attacker often uses information about the target to make the message more convincing.
- Whaling: This is a form of spear phishing that targets high-profile individuals, such as executives or politicians. The attacker often impersonates the target’s colleagues or other trusted individuals.
- Smishing and Vishing: These are forms of phishing that occur via SMS (smishing) or voice call (vishing). The attacker might send a text message or make a phone call pretending to be from a trusted source.
Also read | Chandigarh Woman Loses Rs 80 Lakh in Aadhaar-SIM Card Link Scam
How to Protect Against Phishing Attacks
Here are some tips to protect yourself against phishing attacks:
- Be Skeptical: If an email or message seems suspicious, it probably is. Be wary of messages that ask for sensitive information, especially if they convey a sense of urgency.
- Check the Source: Always verify the source of the message. Check the email address or phone number to make sure it’s from a trusted source.
- Use Two-Factor Authentication: Two-factor authentication adds an extra layer of security by requiring two forms of identification before granting access.
- Keep Your Software Up-to-Date: Regularly updating your software ensures that you have the latest security patches, which can protect against known vulnerabilities that phishing attacks may exploit.
Malware Attacks: Cyber Attacks
Malware, short for malicious software, refers to any software designed to cause harm to a computer system. This includes viruses, worms, Trojans, ransomware, and spyware. Once malware enters a system, it can cause various problems, from stealing sensitive information to causing system crashes.

Types of Malware Attacks
There are several types of malware, each with its unique characteristics and methods of attack:
- Viruses: These are malicious programs that can replicate themselves and spread to other computers by attaching themselves to various programs and executing code when a user launches one of these infected programs.
- Worms: Worms are similar to viruses in their design and purpose. However, they can self-replicate and spread without any user action needed.
- Trojans: Named after the Greek story of the Trojan Horse, these types of malware disguise themselves as legitimate software or are included in legitimate software that has been tampered with.
- Ransomware: This type of malware encrypts the victim’s files and then demands a ransom to restore access to the files.
- Spyware: As its name suggests, this type of malware spies on the user’s activities without their consent or knowledge.
How to Protect Against Malware Attacks
Here are some tips to protect yourself against malware attacks:
- Install Antivirus Software: This software can detect and remove malware from your computer. Ensure it’s up-to-date for the best protection.
- Keep Your Operating System Updated: Regularly updating your operating system can protect against known vulnerabilities that malware might exploit.
- Be Careful with Email Attachments and Downloads: These are common ways for malware to get onto your system. Only open attachments and downloads from trusted sources.
- Use a Firewall: Firewalls can block unauthorized access to your computer system while permitting outward communication.
- Backup Your Data: Regularly backing up your data can help you recover your files if they’re lost during a malware attack.
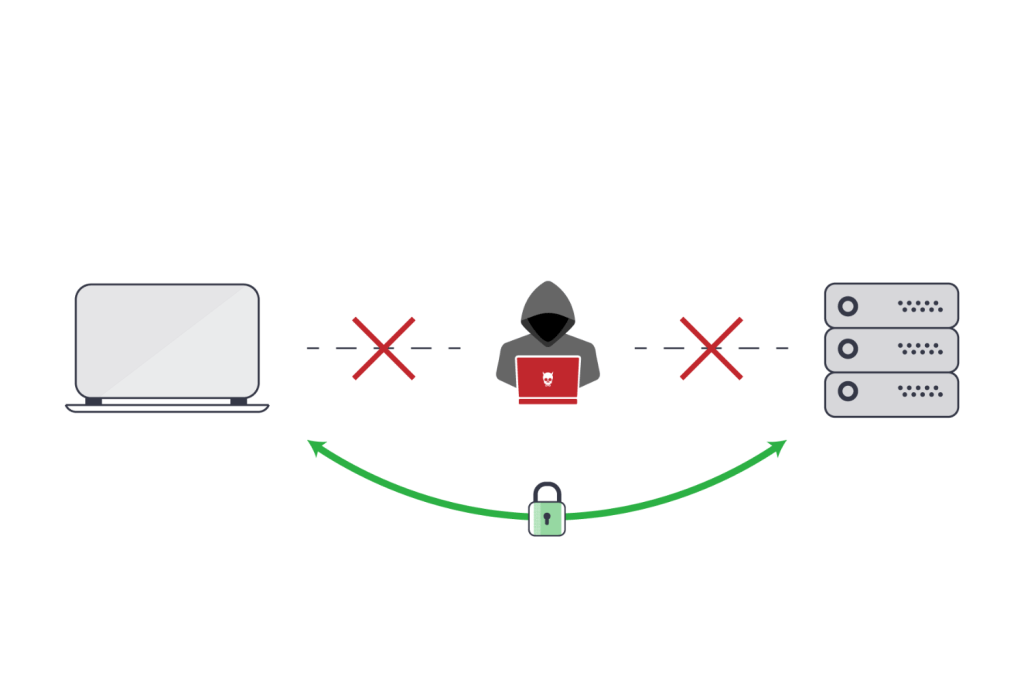
Man-in-the-Middle Attacks
A Man-in-the-Middle attack is a type of cyber attack where an attacker intercepts communication between two parties without their knowledge. The attacker can eavesdrop, manipulate, or steal the data being exchanged. This could happen when you’re connected to an unsecured public Wi-Fi network, where the attacker can easily intercept your data.
Types of Man-in-the-Middle Attacks
There are several types of MitM attacks, each with its unique characteristics:
- IP Spoofing: In this type of attack, the attacker sends IP packets from a false source address to make it appear as if the packets are coming from a trusted host.
- ARP Spoofing: Address Resolution Protocol (ARP) spoofing involves the attacker sending fake ARP messages to an Ethernet LAN. This links the attacker’s MAC address with the IP address of a legitimate computer or server on the network.
- DNS Spoofing: Also known as DNS cache poisoning, this attack involves the attacker redirecting queries to a different domain through corrupt DNS data.
- HTTPS Spoofing: In this attack, the attacker provides a fake SSL certificate to the victim’s browser, making it appear as if a secure connection has been established.
- Wi-Fi Eavesdropping: This involves the attacker intercepting data transmitted over a Wi-Fi network. This is particularly common in public Wi-Fi networks.
How to Protect Against Man-in-the-Middle Attacks
Here are some tips to protect yourself against MitM attacks:
- Use Encrypted Connections: Always use HTTPS for browsing. This ensures that your data is encrypted and cannot be easily intercepted.
- Secure Your Wi-Fi: Make sure your Wi-Fi network is secure. Use strong passwords and consider using a VPN for additional security.
- Be Wary of Public Wi-Fi: Public Wi-Fi networks are a common target for MitM attacks. Avoid transmitting sensitive data when connected to a public network.
- Keep Your Devices Updated: Regularly updating your devices ensures that you have the latest security patches, which can protect against known vulnerabilities that MitM attacks may exploit.
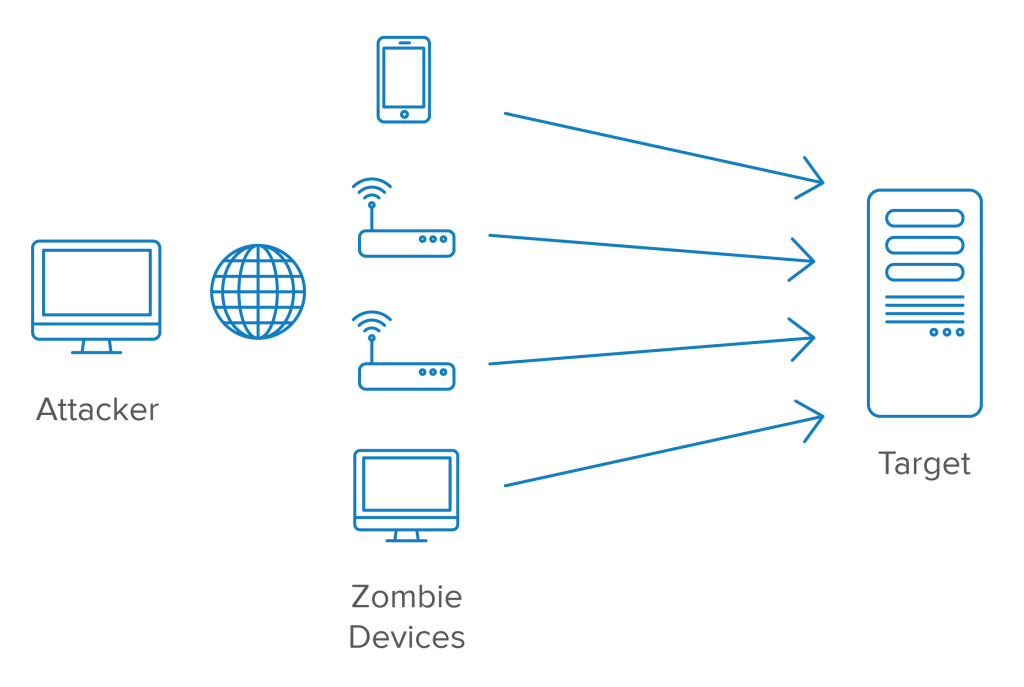
Denial-of-Service Attacks
A denial-of-service (DoS) attack aims to make a system or network unavailable by overwhelming it with traffic. This prevents legitimate users from accessing the service. A variant of this attack, known as a distributed denial-of-service (DDoS) attack, involves multiple compromised systems attacking the target simultaneously.
Types of Denial-of-Service Attacks
There are several types of DoS attacks, each with its unique characteristics:
- Volume-Based Attacks: This includes UDP floods, ICMP floods, and other spoofed-packet floods. The attack’s goal is to saturate the bandwidth of the attacked site, and magnitude is measured in bits per second (Bps).
- Protocol Attacks: This includes SYN floods, fragmented packet attacks, Ping of Death, Smurf DDoS, and more. This type of attack consumes actual server resources, or those of intermediate communication equipment, such as firewalls and load balancers, and is measured in packets per second.
- Application Layer Attacks: This includes Slowloris, Zero-day DDoS attacks, DDoS attacks that target Apache, Windows, or OpenBSD vulnerabilities, and more. Comprised of seemingly innocent and legitimate requests, the goal of these attacks is to crash the web server, and the magnitude is measured in Requests per second.
How to Protect Against Denial-of-Service Attacks
Here are some tips to protect yourself against DoS attacks:
- Install and Maintain Antivirus Software: Antivirus software can detect and prevent DoS attacks before they harm your system.
- Firewalls: Firewalls can limit traffic to your network and signal you when your system is being attacked.
- DDoS Protection Services: Companies that are at high risk for DDoS attacks often use third-party DDoS protection services to guard against attacks.
- Keep Your System Updated: Regularly updating your system ensures that you have the latest security patches, which can protect against known vulnerabilities that DoS attacks may exploit.
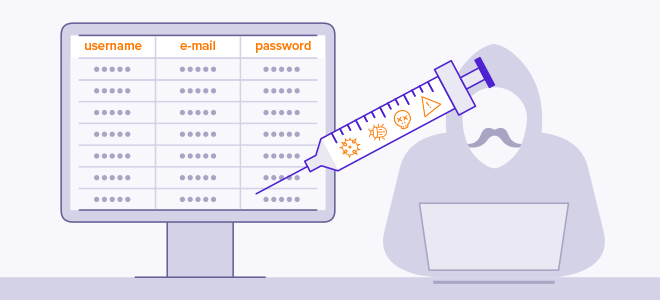
SQL Injection Attacks: Cyber Attacks
An SQL Injection attack is a type of cyber attack where an attacker inserts malicious SQL code into a query. The malicious data then produces unexpected and potentially harmful results, such as revealing sensitive information, modifying the data, or even executing administration operations on the database.
Types of SQL Injection Attacks
There are several types of SQL Injection attacks, each with its unique characteristics:
- Classic SQL Injection: This is the most common type of SQL Injection. The attacker injects malicious SQL code into user input that is part of an SQL query.
- Blind SQL Injection: In this type of attack, the attacker asks the database true or false questions and determines the answer based on the application’s response.
- Time-Based Blind SQL Injection: Similar to blind SQL Injection, this attack asks the database a question that will cause the database to wait before responding. The attacker can then determine the answer based on the amount of time it takes for the application to respond.
- Out-of-Band SQL Injection: This type of attack occurs when an attacker is unable to use the same channel to launch the attack and gather results.
How to Protect Against SQL Injection Attacks
Here are some tips to protect your web application against SQL Injection attacks:
- Use Prepared Statements: Prepared statements ensure that an attacker cannot change the intent of a query, even if SQL commands are inserted by an attacker.
- Use Stored Procedures: Stored procedures can provide the same level of protection as prepared statements.
- Escape User Input: If you need to use user input within SQL queries, make sure to escape the input to ensure it’s safe to use.
- Least Privilege: Only assign the minimum privileges necessary to the database account used by the web application to reduce the potential damage if an SQL Injection attack occurs.
Zero-Day Exploits: Cyber Attacks
A zero-day exploit is a cyber attack that occurs on the same day a weakness is discovered in software. Because the vulnerability is unknown to those who should be interested in mitigating the vulnerability (including the vendor of the target software), the exploit can cause significant damage.

Impact of Zero-Day Exploits
Zero-day exploits can have severe consequences, as they take advantage of vulnerabilities that are unknown to others or the software vendor. This gives the attacker the upper hand. They can lead to significant data breaches, financial loss, and damage to an organization’s reputation.
Examples of Zero-Day Exploits
One of the most famous zero-day exploits is the Stuxnet worm. It was a malicious computer worm first uncovered in 2010 but thought to be in development since at least 2005. Stuxnet targets supervisory control and data acquisition (SCADA) systems and is believed to be responsible for causing substantial damage to the nuclear program of Iran.
Also read | Top 10 best Chatbots for Small Businesses in 2025
How to Protect Against Zero-Day Exploits
Protecting against zero-day exploits can be challenging due to their unknown nature. However, some strategies can help mitigate the risk:
- Use Antivirus Software: Antivirus software with heuristic capabilities can detect and defend against zero-day exploits.
- Keep Software and Systems Updated: Regularly updating your software and systems ensures that you have the latest security patches.
- Employ Network Segmentation: By segmenting your network, you can prevent an attacker from easily moving laterally through your network if they exploit a zero-day vulnerability.
- Implement a Strong Security Policy: A strong security policy that includes regular audits, user training, and incident response can help protect against zero-day exploits.
Understanding the different types of cyber-attacks can help individuals and organizations better protect themselves in the digital world. Remember, the best defense against cyber attacks is a good offense: stay informed, use strong, unique passwords, keep your software up-to-date, and be cautious when providing personal information online. Stay safe!

