Decryptor for Black Basta Ransomware, In a significant development in the cybersecurity landscape, researchers have released a free decryptor for the notorious Black Basta ransomware. This is a major breakthrough that could help numerous victims recover their encrypted data without paying a ransom.
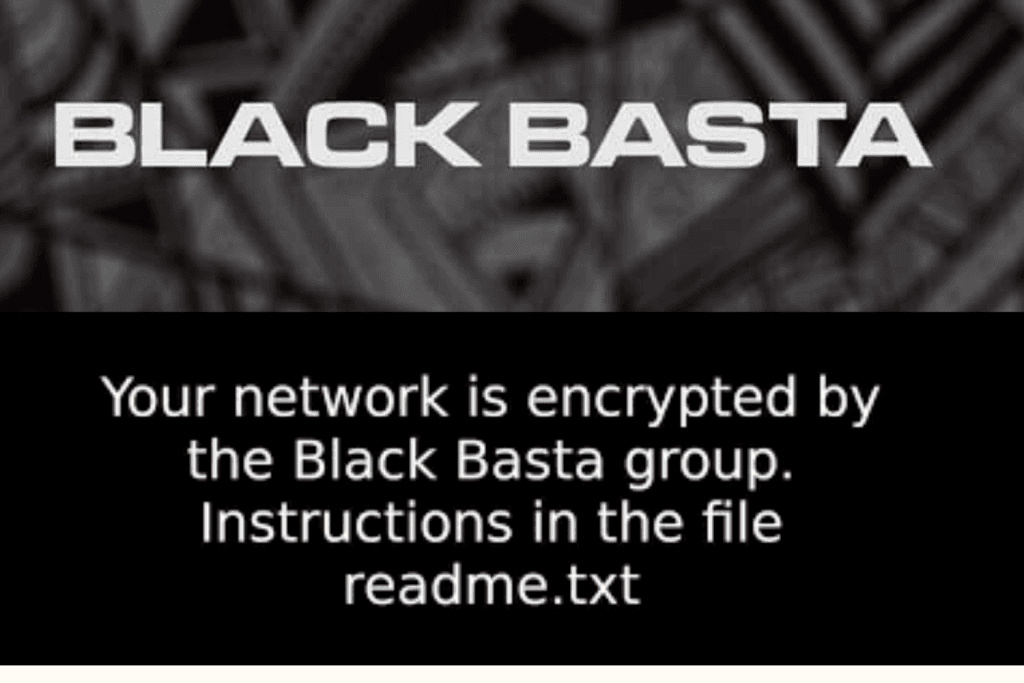
Black Basta Ransomware
Black Basta is a type of ransomware, malicious software that encrypts victims’ files and demands a ransom for their release. It has been a prolific threat in the cyber world, causing significant damage to individuals and organizations alike.
Impact of Black Basta Ransomware:
Over the past several months, Black Basta has targeted individuals and organizations across various sectors, ranging from small businesses to large enterprises. The financial and emotional toll on victims has been substantial, with the ransom demands often reaching exorbitant amounts. The release of the free decryptor is a beacon of hope for those who have fallen prey to this malicious software, offering a lifeline to recover their invaluable data.
Black Basta Buster
Researchers from SRLabs have released a free decryptor for Blackasta ransomware, allowing some victims of the group to decrypt files without paying a ransom. The decryptor helps victims decrypt files that attackers encrypted in November 2022 and December 2023.
The decryptor, called Black Basta Buster, exploits a flaw in the encryption algorithm used in older versions of the Black Basta group’s ransomware. The group fixed the bug in mid-December, probably after its discovery, so it won’t affect the most recent attacks.
During the period the decryptor worked, the gang carried out 153 known attacks, where victims refused to pay a ransom and appeared on Black Basta’s dark web data leak site. BlackBasta first appeared in April 2022 and is a regular entry in the top 5 most active ransomware groups in our monthly ransomware reviews. Among others, the ransomware has been used to attack organizations like Canada’s Yellow Pages and German arms producer Rheinmetall.
decryptor has a few restrictions
The decryptor has a few restrictions due to the nature of the flaw it exploits. Files below the size of 5000 bytes cannot be recovered. For files between 5000 bytes and 1GB in size, full recovery is possible. For files larger than 1GB, the first 5000 bytes will be lost but the remainder can be recovered. The decryptor only works on one file at a time and your best chances are on virtual machine disks. According to SRLabs, virtualized disk images “have a high chance of being recovered, because the actual partitions and their filesystems tend to start later. So the ransomware destroyed the MBR or GPT partition table, but tools such as “test disk” can often recover or re-generate those.”
Files can be recovered if the plaintext of 64 encrypted bytes is known. The easiest way to establish this is to find a sequence of zeroes in the file. It may be possible to decrypt large files that don’t contain large enough chunks of zero bytes, but you will need an unencrypted version of the target file. In many cases, this will defeat the purpose of decryption, but there may be edge cases where you have a previous version of the target file that meets the requirements but does not hold the information you want to decrypt.
On the GitHub pages, you will find several Python scripts to help you with the recovery of the encrypted files. Interested parties can find instructions on how to use them in the readme file. This is not an easy process and certainly not something we would recommend using for every encrypted file. Each victim will need to weigh up how useful it is to them.
Also read | 5 Practical techniques for effective cyber threat hunting
Protecting Against Ransomware:
It’s better to avoid malicious encryption if you can, so here are some pointers.
- Be careful with email messages. Email spam is a primary spreading vector for a lot of malware types, not only ransomware. By reviewing the sender and the attached file/link, you can avoid getting infected.
- Install the latest software and firmware updates. Vulnerability exploitation is hackers’ bread and butter when it comes to lateral movement and payload deployment. The majority of exploitation happens after the vulnerability becomes public and gets patched – so do not hesitate to update the programs you use.
- Avoid using cracked software. Cracks are an ideal breeding ground for different malware due to the mandatory interference with the program’s code. This spreading approach has existed for several decades and plagues both home users and workstations.
- Employ using reliable anti-malware software. By having anti-malware software you ensure that malware will not slip through the method you are not aware of. A well-designed security solution will detect and remove even the newest malware with heuristic and AI detection systems. GridinSoft Anti-Malware is a program that offers such functionality – give it a try.
In conclusion, While this is a significant victory, it’s important to remember that the best defense against ransomware is prevention. Regularly updating software, backing up data, and practicing safe internet habits are crucial steps in protecting against ransomware attacks.
The fight against ransomware is far from over, but the release of the Black Basta decryptor is a positive step forward. It serves as a reminder that through persistent effort and collaboration, we can push back against these cyber threats.